
 |

Latest version: USB Lock RP V.13.932 – May 23rd, 2025.
(Includes Client v13.937 with Auto-Encryption Security Reinforcement)
USB Lock RP V.13.928 – May 6th, 2025. (Includes Client v13.934 with Automatic security Hardening)

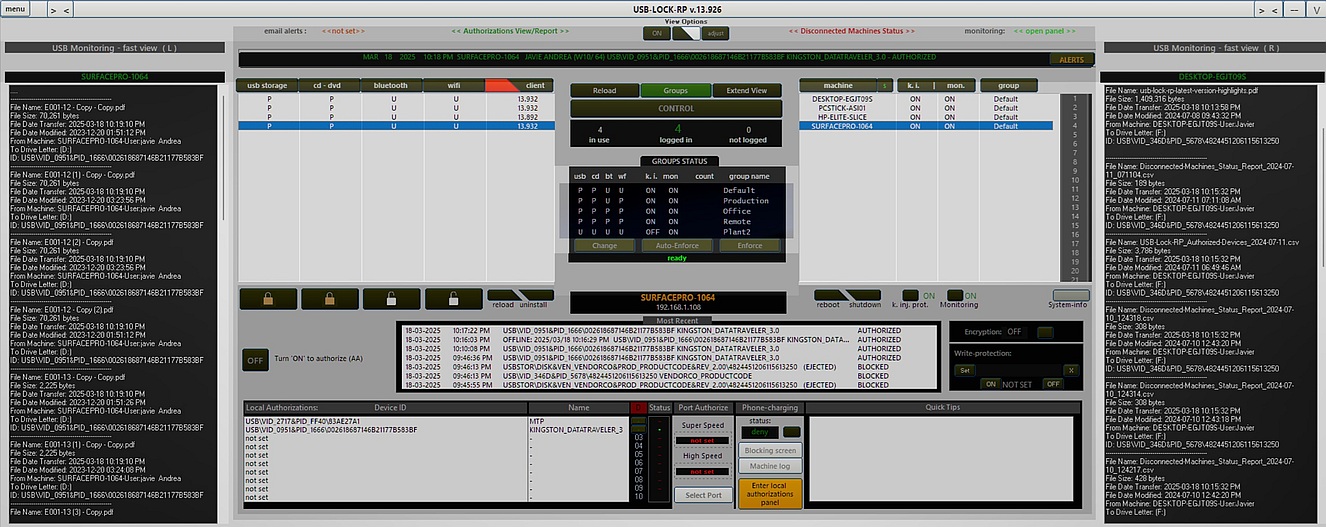
USB Lock RP V.13.926 – March 18th, 2025.
Light-mode/Dark-mode Control Interface
USB Lock RP V.13.924 – February 16th, 2025.
Specific USB Port Authorization & Control:
USB Lock RP V.13.889 – Published as demo January 17th, 2025.
USB Lock RP V.13.878 – January 8th, 2025.
Real-Time Multilingual Support:
USB Lock RP V.13.838 – July 8th, 2024.
Disconnected Machines Enhanced Visibility:
Enhanced Approved Devices Visibility:
USB Lock RP v.13.829 - May 22, 2024.
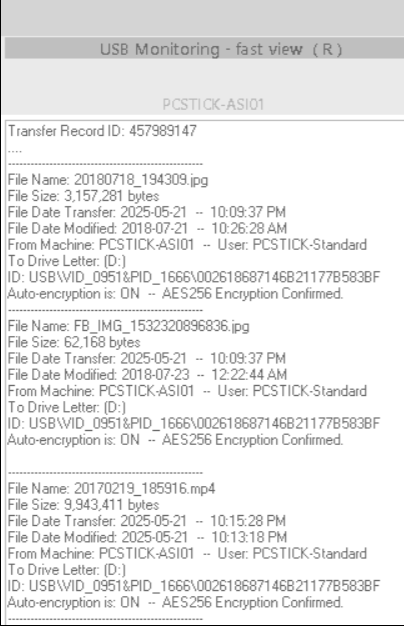
New USB File transfer monitoring & Email Alerts.
USB Lock RP v.13.824 - April 16th, 2024.
New Local Authorization Panel: Offers 4 easy ways to authorize USB devices.
USB Lock RP v.13.531 - April 3rd, 2024.
USB Lock RP v.13.522 - December 21st, 2023
USB Lock RP v.13.449 – October 19th, 2023
Offline alert logs:
Blocked and authorized alert events happening while a client is disconnected from the control
for any reason are automatically retrieved when the client reconnects to the control.
OFFLINE alerts can be found normally on the machine alerts log and the most recent alerts. (Same as other per machine alert logs).
Offline alerts will additionally show the event date/time and will be marked as OFFLINE.
Show in real-time when any locally authorized removable storage device is in use(connected/disconnected)
Function to query if a client is blocked at any time.
New interface layout includes Quick tips visor that informs about the functionality of all elements on mouse over.
Per machine right-click on main network list to move machines and apply:
Group Settings, Group authorized devices and Group master password.
(In one action)
Removable storage and smartphones friendly name column.
(Local authorizations)
Devices friendly name also included on alert logs and reports.
Color coded alerts arrival: Allows to easily call the attention on events at a glance.
New Bulk license recovery function panel:
Allows to massively recover licenses from unused machines.
New Clients Update function panel:
Allows to massively update client’s version from control-side.
New MTP blocking behavior:
Allows unauthorized Smartphones to be connected for-charging-only without
blocking.
(Reverted, unauthorized Smartphone charging is no longer allowed starting Version 13.122)
New "system-mode" 24/7 real-time management and enforcement capability.
Function: To auto-start the control in system-mode while an admin-mode control is not running.}
Characteristics:
- system-mode and admin-mode start stop log.
- capacity to configure the service from admin-mode.
- capability to set auto-enforce group setting while on system-mode.
USB Device tracking alert function alerts the Control administrator in real-time upon the connection of any specific USB ID to any client in the network.
This function can be used for intrusion detection or to test behavior of employees regarding policy in reference the connection of unknown devices to company computer peripheral ports. (Control-side update available)
Specific Read-Only Function:
Write-Protects Specific USB Drives while other authorized USB drives can be full access on the same machine. (While unauthorized USB drives continue to be blocked)
Characteristics:
File transfer to write-protected USB drives are interrupted at Operating System level.
Other USB drives authorized as Full access can be used simultaneously)
Read-Only Policy is informed to the user upon device insertion
Read-Only Policy violation attempts are reported to the Control in real-time.
Any of the 10 local authorizations can be made Read-Only.
Selective Read-Only behavior can be turned ON/OFF in real-time without requiring the disconnection of the device.
While Read-Only is ON, Files cannot be transferred, modified or deleted and the USB Drive cannot be formatted.
Groups Status at a Glance. (Main Interface)
Groups Enforce: Enforces Settings. (One Pass, to all logged machines) (Main Interface)
Groups Auto-Enforce Settings: (Continuous watch over Group Settings) (Main Interface)
Note:Auto-Enforce is the New Recommended Operation Mode.
Note:When settings are changed, not logged machines will automatically receive setting once they are back.
New Network status report includes Groups Protection Status and Auto Enforce Status.(Menu)
Machine history by double click. (Double click on any machine on the main network list to view its history)
Friendly Name Query:
Double click device IDs on local Authorizations list to view Device friendly name.
Double click device IDs on most recent Alerts list to view Device friendly name. (alerts containing USB IDs)
Double click device IDs on any machine history list to view Device friendly name. (alerts containing USB IDs)
Keystroke Prevention and Monitoring columns on main interface network list.
Remote desktop compatibility, auto adjusts to accommodate different screen resolutions.
Left and right side panels for USB Monitoring at a glance.
Groups count: Counts group members On Enforce or Auto-Enforce. (On Group Status Center Panel)
Resolves Issues with Remote Desktop (RD) work area resolutions higher 1920 x 1080
Improved auto adjustment on Remote Desktop (RD) changes
Improved alerts log and per machine history logs: Logs now extend completely for better use of screen work-area.
New enhanced viewing options:
Allow to change background, show columns, and adjust transparency.
Unicode compatible
Automatic Authorizations mode: The perfect solution to automatize implementation.
No need to re-plug authorized devices to use them.
Can use as many authorized devices as needed simultaneously.
Flawless, 100% reliable and consistent client side behavior.
Immediate alerts, 100% reliable.
SIEM Interoperability.
Automatic report scheduling.
Groups Management:
Groups building. (Massively moves machines to Groups)
Group level, Real-time Set and deploy security policy of all sectors simultaneously.
Group level, Real-time Set and deploy authorized devices. (Capacity: 60 spots per group (Complete ID or VID/PID only)
Group level master password.
New function to troubleshoots authorization issues to any client with one click from the control.
Re-sets the ground from where the program starts detecting. Many internal card readers report to the operating system as removable.
New Authorization part GUI. (Less complicate, all authorized device IDs always visible at a glance.)
Solves possible issue with Composite drives being silently dismounted after being authorized.
New Local Authorizations report.
USB blocking behavior change for USB Mass sorage devices:
Note:Prior to this version with an Authorized device connected an functioning the connection of an unauthorized device would block both connected devices and require the removal of both devices before the authorized device can be used.
Note:The new version will just selectivelly block the unauthorized device and removing it will allow regaining access and the authorized device continues functioning without requiring removal.
Includes: Groups Auto creation + Group renaming + protection of sectors based on groups.
Improved Control Interface (Larger resolution)
Improved authorized device function at client side.
Corrected issue with mouse over for tips and other minors.
Protects against UASP devices (USB Attached SCSI Protocol) ( All systems running Windows 10 or Windows Server 2016 could be vulnerable if not upgraded).
Protects against Keystroke injection attacks, by Badusb devices such as USB Rubber Ducky. This devices have been reported to be used against Banks worldwide (All client operating systems could be affected if not updated)
Encryption of all critical data used by the program at Control side and Clients side (example: Authorized devices hardware IDs) This is required so authorized devices IDs can only be read from the Control application.
Improvements in connectivity with clients.
Improvements on device authorization function.
Improvement on Thumb drives monitoring function.
Improved Control Interface.
Improvements on auto-whitelisting modern MTP devices such as finger print readers and printers.
Note: On the older version this devices would be blocked causing issues.
Master password function to allow one-off authorization using password (USB, MTP, UASP) from client side when Communication with control is unavailable (this is useful for troubleshooting or on special situations in which the need to authorize a device is required for example on a laptop that is disconnected from the network.
New on this version:
One of the main differences is that this version uses AES 256 encryption to protect all program keys and transmissions.
Note: AES256 implementation is CBC MODE variable key, variable initiation vector implementation)
Resolves issues that could appear with internal mtp finger print scanners.
Provides superior monitoring features for Thumb drives (You can turn that ON or OFF)
Provides superior Encryption and Decryption mechanism for Thumb drives (Fully automatic and personalized) (can be turned ON or OFF)(AES 256)(no need for password)
Provides functionality to enter password at alert blocking screens (USB and MTP) to recover from undesired blocking or one off authorizations (password input box appears if alert remains more than 20 seconds) (the default password for this blocking screens is: usblockrpD) (to change this password deploy a new one from the control network authorization panel.)
Newer Interface.
60 network wide authorizations.
Clients report their version to the administrative control
Clients report their operating system also on alerts
All users logged are reported
Demo is non expiring
Capacity is for 3 clients.
Central reporting function
Improvements on reports.
New Operating Manual:
USB 3 authorizations at USB 3 super-speed, (before they were authorized only at USB 2 speed)
Central reporting, allows for multiple control setups (Un obtrusive central reporting).
Auto Protect this will allow to protect all sector on a client after a select period of time.
Recent Alerts: most recent alerts per client visible at a glance.
Authorizations visible at a glance.
MTP specific authorizations capability (local and network).
Elevate to network authorizations MTP and USB (drag & drop)
Real time show not logged Pcs
Remove (out) old Pcs from list (drag & drop)
Compact mode allows control to run under minimal interface.
Software Install and uninstall alert/monitoring
Full screen mode with the personalization logo.
Files usb storage monitoring list auto update.
Improved Status report
Lower system resources consumption
Multi-monitor blocking:
This update ensures all monitors on a client are covered by alert screen.
Internal card reader issue:
This update solved issues presented by internal cardreader using generic drivers.
Blocking alerts:
New alert screens design.
Auto email function:
Supports SMTP TLS or SSL transmission protocols.
Get automatic realtime email alerts of portable devices connection to any network station.
Larger Administrative control interface.
Support for blocking multi-monitor.
Higher hierarchy management
Reports authorized usb file extractions to the central control and to an email within your domain
Digitally signed installers
Allows 30 groups of devices or specific devices to be authorized at network level (in all client PCs).
Deployment of network wide authorizations is in real-time and it's done automatically to not connected PCs (as soon as they connect).
Allows for up to 10 devices to be authorized on each client PC.
Reports who is not connected on the network
Capable of ordering network list by name, IP or protection status.
System information reports in real-time all authorized devices on any client.
Also provides capability for distribution of portable protectors to protect information inside authorized usb devices, auto encryption and portable protectors centralized password management (with the optional- RPE module).
Reports in real-time:
System information, installed software, installed windows updates and security patches, and running processes on any client.
USB Aware now also reports print jobs.
Alerts include device PID and logged user.
USB Aware reports also exact size of extracted files.
Allows two authorizations per client machine (and better management)
Function to determine who is not connected
Machine history logs also include the alerts incoming to that machine and authorization logs.
The main Control list is linked to the usb aware panel. Selecting usb aware from the control will take you directly to see the name of extracted files.
USB Aware:
To monitor names of usb extracted files now also monitors smartcards.
Protection scope is expanded to smartcards and all removable storage devices (not only usb)
Fast PC lookup function to easily find PCs on the network.
Wireless protection scope also includes infrared devices to prevent IrDA mobile phone file extractions. (Not only Bluetooth)
New auto-safely remove device alert screen.
Control access is password protected
Legal Notice:
USB-Lock-RP™© software is TradeMark and Copyright © 2004-2025 Advanced Systems International sac, All rights reserved